Social engineering is the main underlying tactic used for phishing of all types. Whether it’s email phishing attacks, social media phishing, “vishing” (phone scams), or another type of scam.
The definition of social engineering in a cybersecurity sense is “the use of deception to manipulate individuals into divulging confidential or personal information which may be used for fraudulent purposes.”
Social engineering is at the heart of most cyberattacks since most of them originate through phishing, this makes it the biggest danger to network security and protection of sensitive personal information.
96% of social engineering attacks are delivered through email.
Key Social Engineering Tactics
There are two key tactics deployed in most social engineering attacks. These are emotional triggers and earning trust.
Emotional triggers designed to get users to react to a message without thinking include:
- Urgency (e.g., “Your account has been put on hold until you take action”)
- Fear (e.g., “You must log in and update your password now or risk leaving your account vulnerable”)
- Confusion (e.g., “Did I really make an order on Amazon and just forgot? Why did I get this order receipt?”)
- Excitement (e.g., “Attached is a purchase order for a large amount of your product that we need right away.”)
- Flattery (e.g., “You’ve got great taste in clothing, I can tell from your social media photos)
Trust is an important ingredient in a social engineering attack because the more the person trusts the message or the message sender the more likely they will be to believe it’s legitimate.
Tactics used to gain trust include:
- Spoofing the domain in the email address to be one that is familiar to you
- Using personalization in the email (i.e., adding your name, title, location, etc.)
- Using logos and signatures of legitimate companies (like the email example below)
- Paying you a compliment on social media
- Mentioning liking the same band, music, festival, etc. as you do to get you to put your guard down
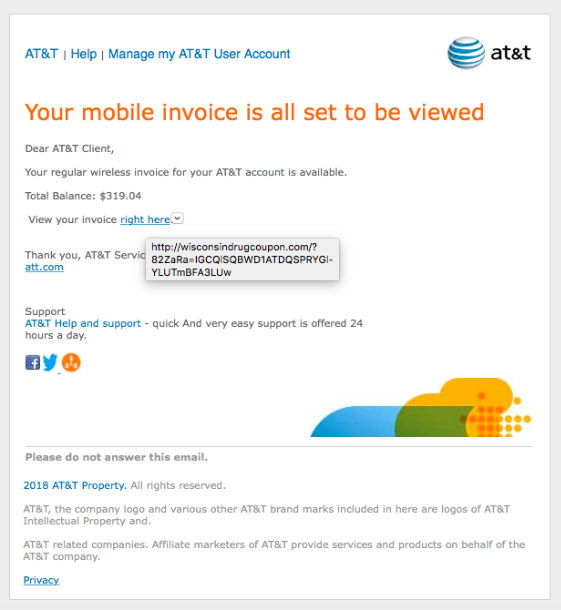
This phishing email is an example of spoofing the logos and signature of a legitimate company to gain trust for a phishing attack message.
What Do These Types of Attacks Look Like?
Because social engineering is a tactic used in multiple cybercrimes and online attacks, you’ll see it used in multiple ways.
Baiting
This would be creating a trap and then getting you to fall into it. Such as sending you a phishing email that says you need to update your Amazon account credentials, which leads you to a faked login page (the trap) designed to steal your password.
Pretexting
This type of attack would involve something that looks innocent at first and then ends up being malicious. Like an ad online for a free antivirus program that asks for your credit card details at the end of the form you need to fill out to get it.
Phishing
Most people are familiar with phishing. It’s the use of emails, text messages, social media, or phone calls to trick someone into taking some type of action.
Quid Pro Quo
This attack offers something to you, which makes you less suspicious. For example, you could see a free app offering a map of the best coffee shops around the world, but that app masks spyware that is installed when you download it.
Ways to Protect Yourself from Social Engineering Attacks
Be Wary of “Fast Friends” on Social Media
Many criminals will work social media as their prime hunting ground for finding unsuspecting people. They will try to befriend you using things they’ve found on your social media feed and then once they gain your trust, they spring their trap.
Beware of anyone befriending you out of the blue on social media. Be sure to do your research and check their profile thoroughly. Often a quick profile check can turn up an empty profile full of nothing put profile pictures (that most likely aren’t even of the person).
Use Multi-Factor Authentication on All Cloud Accounts
One social engineering tactic is to take over someone’s Facebook or other social account and then post as that person to scam their friend connections.
You can avoid having this happen to your accounts by enabling multi-factor authentication. This also protects your accounts should a phishing attacker manage to get your login credentials from a spoofed login form.
Use Cybersecurity Protections (Email Filters, Anti-malware, etc.)
Good cyber hygiene is an important safeguard against these social engineering attacks. This includes using protections such as:
- Email/spam filters
- DNS filters
- Anti-malware
- Device firewall
- Mobile antivirus
Get Help Building Strong Defenses Against Cyberattacks
Be proactive about social engineering to keep your company and employees secure. AhelioTech can help your Columbus area business with protections designed to reduce the number of phishing emails that make it through to users, and much more.
Contact us today for a free quote. Call 614-333-0000 or reach out online.
.





